A new report from Eclypsium, an enterprise firmware security, flagged three major tech companies for vulnerabilities.
In the report, “Screwed Drivers,” the company found that more than 40 drivers from 20 different manufacturers have insecure drivers. Among the vendors include AMD, NVIDIA, Huawei, Toshiba, Intel, and ASUS.
But what’s alarming about the report is that all the drivers deemed vulnerable were already certified by Microsoft. That means a certification doesn’t necessarily mean it’s secure. In fact, it provides the attacker with a backdoor into the user’s computer due to “elevated privileges.”
The company also contacted Microsoft to find a way to address the problem, which includes blacklisting.
The company explained that a bad driver will give the attacker user privileges, which give access to the kernel. The malware installed will then look for any vulnerability in the system to gain control over the whole PC.
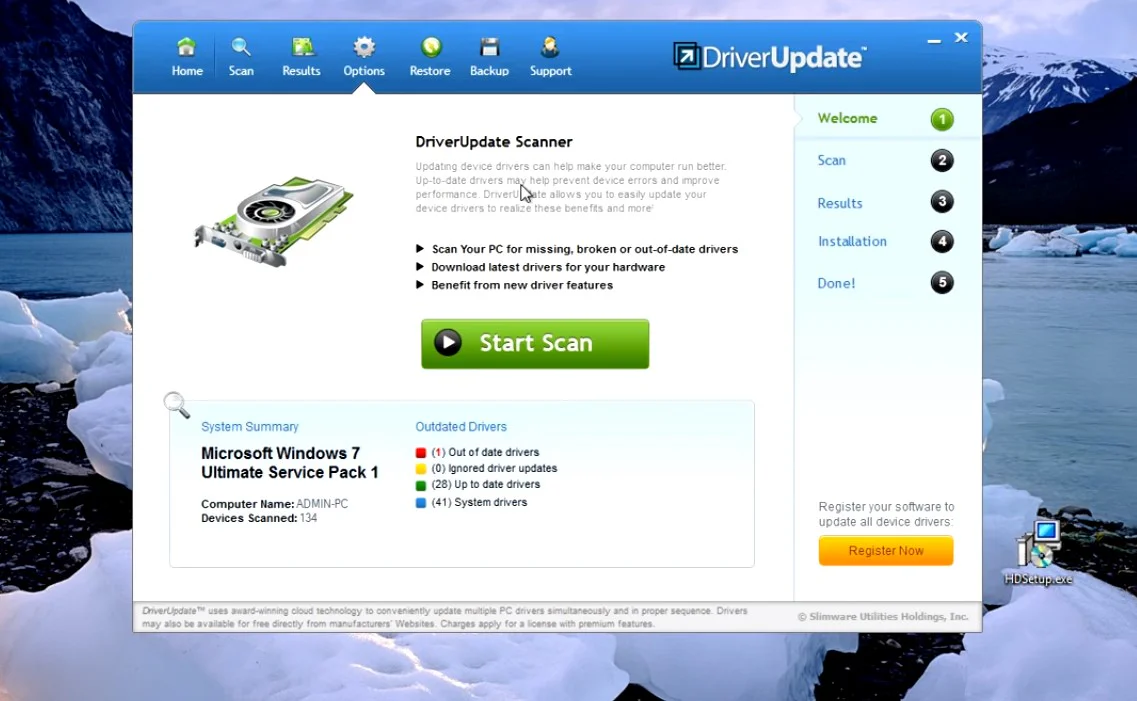
Eclypsium cited the LoJax malware, which could not be eliminated even if you install the whole operating system. It spreads out to the other device components and the system firmware. Some malwares interact with the network adapters, GPUs, CPUs, and other components. Here’s a simple tutorial on how to remove a PUP.DriverUpdate, although others might not be as simple.
The problem is that most drivers enable firmware updates, which give them the necessary tool to make changes to the system.
The vulnerable drivers cited in the analysis enable them to act as a proxy to access hardware resources. These include write and read access to the chipset or processor, control registers, model-specific registers, kernel VR, and RAM.
Instead of being contained in the user mode, the driver allows the attacker to move into the OS kernel mode. This is an extraordinary access that gives them the ability to attack not just the OS, but also the hardware and firmware, and BIOS.
The Screwed Drivers report then highlighted the common misconception–a Microsoft certificate doesn’t always mean secure. It said that most of the attack doesn’t involve unsanctioned or unlisted drivers but actually from trusted vendors. Microsoft even imprinted its signature of approval through a certificate on these drivers. The company then said that both Microsoft and the vendors need to heighten their security and vigilance against the vulnerabilities.
The problem is that there’s no mechanism in place to keep the OS from loading these vulnerable drivers. And once they are installed, the drivers will take root in the device unless uninstalled or successfully updated.